
Why the Next Generation of CISOs Need Business Skills as Well as Technical Expertise
Becoming A CISO – Then Vs. Now For years, the career path to becoming a Chief Information Security Officer (CISO) looked fairly predictable. Gain experience
Our unique program allows our graduates to lead their peers to strategically and effectively manage cybersecurity risks in their organizations.


Becoming A CISO – Then Vs. Now For years, the career path to becoming a Chief Information Security Officer (CISO) looked fairly predictable. Gain experience
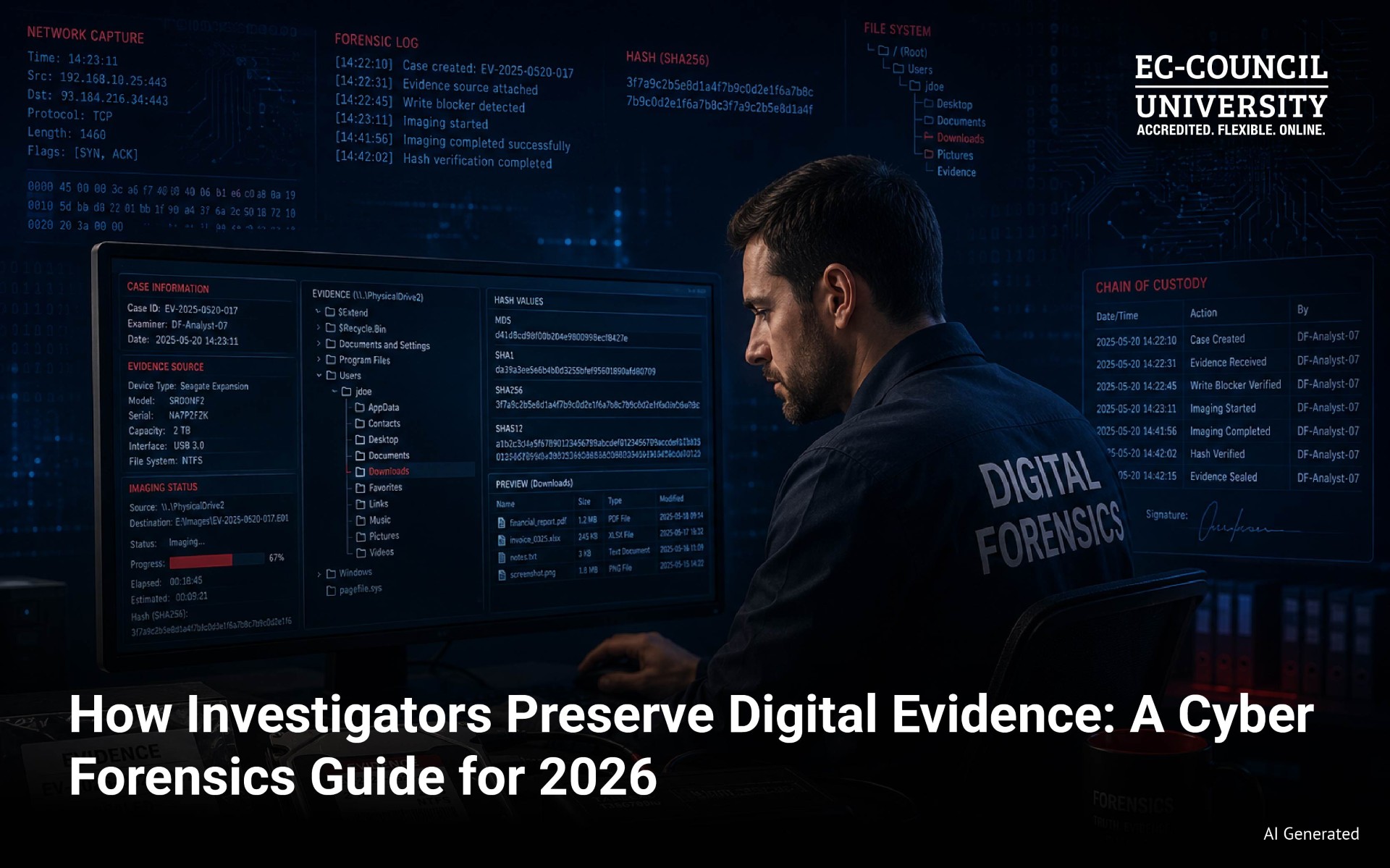
When digital evidence enters an investigation, the clock starts immediately. Every action taken on a device, every file opened, every second of delay changes what

Cybersecurity is no longer a field where broad knowledge carries you to the top. The roles commanding serious compensation in 2026 belong to specialists. Security

Digital forensics has moved well beyond the crime lab. Today it serves incident response teams, litigation support, and corporate intelligence. Organizations in finance, healthcare, and

What Is Disaster Recovery in Cybersecurity? Disaster recovery (DR) in cybersecurity refers to the processes, policies, and technologies used to restore IT systems, data, and

Thinking of a Career Path After Military Service? If you’re a U.S. Military veteran, odds are that you’ve considered online education to help you pursue
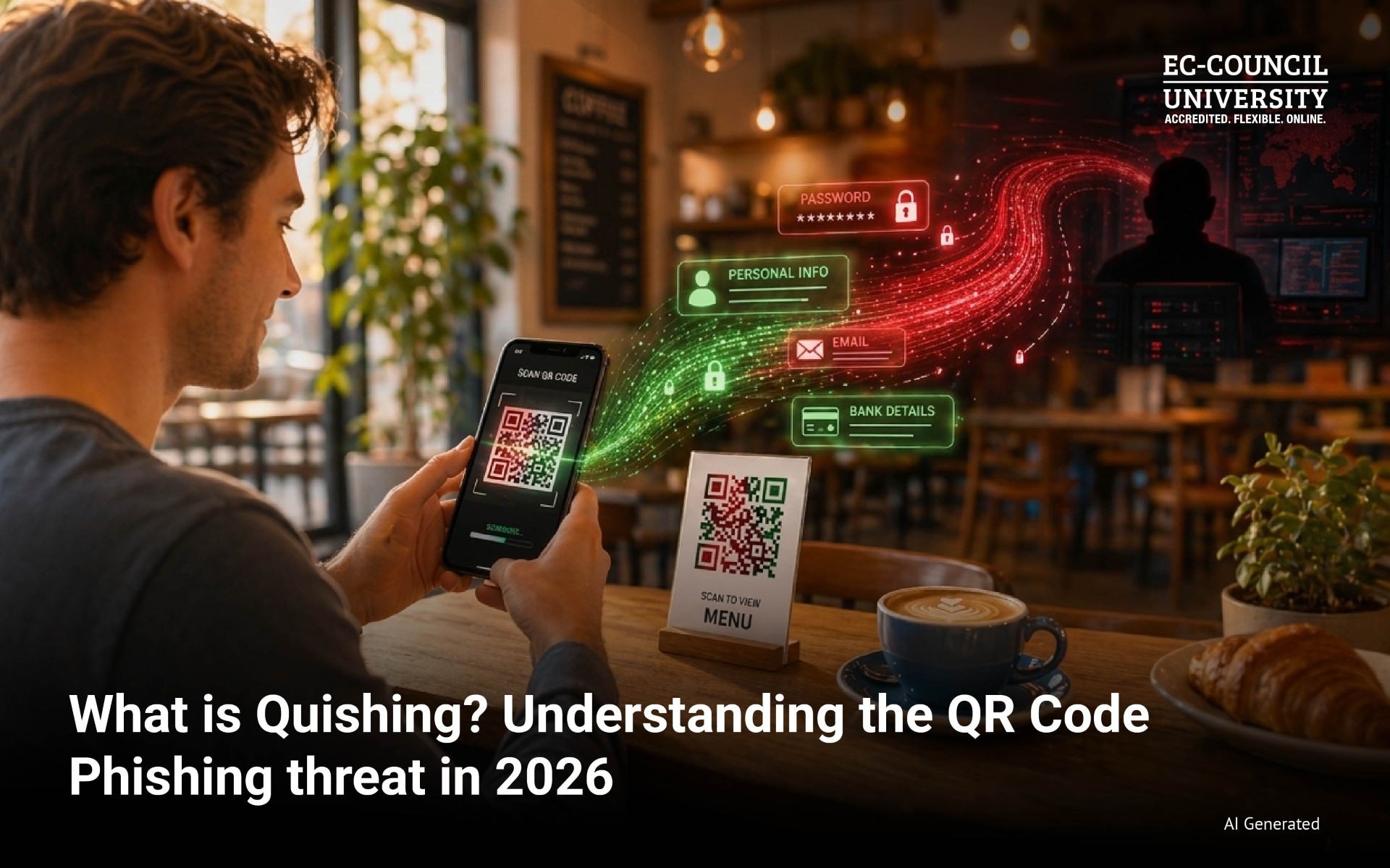
Quishing is not an emerging threat anymore. It is here, and it is scaling fast. What started as a fringe attack technique has quietly grown
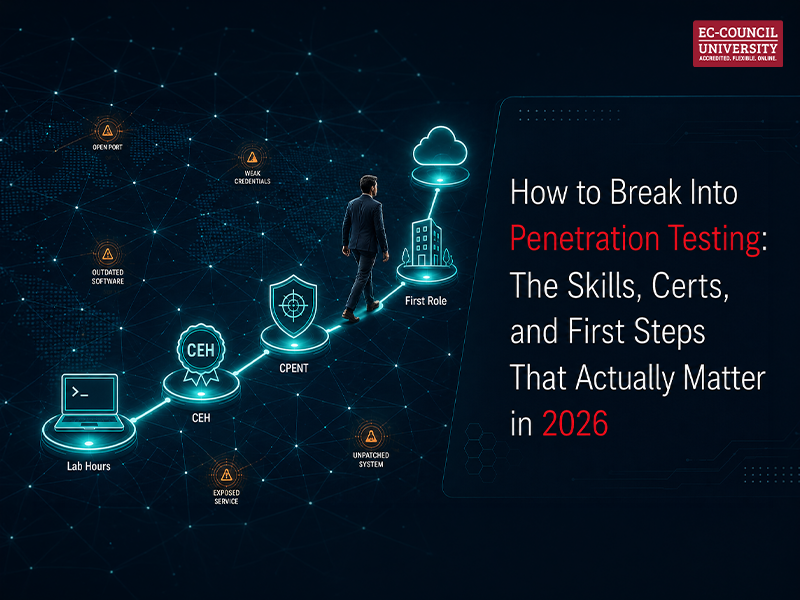
Penetration testing is one of those careers that sounds clear from the outside. You simulate attacks. You find vulnerabilities. You get paid well to think

The Rise of Prompt Injection as a Cybersecurity Threat As organizations race to embed large language models (LLMs) into customer service platforms, enterprise tech stacks,

Cybersecurity is not a static field. It never was. But the pace at which AI is reshaping it has forced a specific question for anyone

Becoming A CISO – Then Vs. Now For years, the career path to becoming a Chief Information Security Officer (CISO) looked fairly predictable. Gain experience
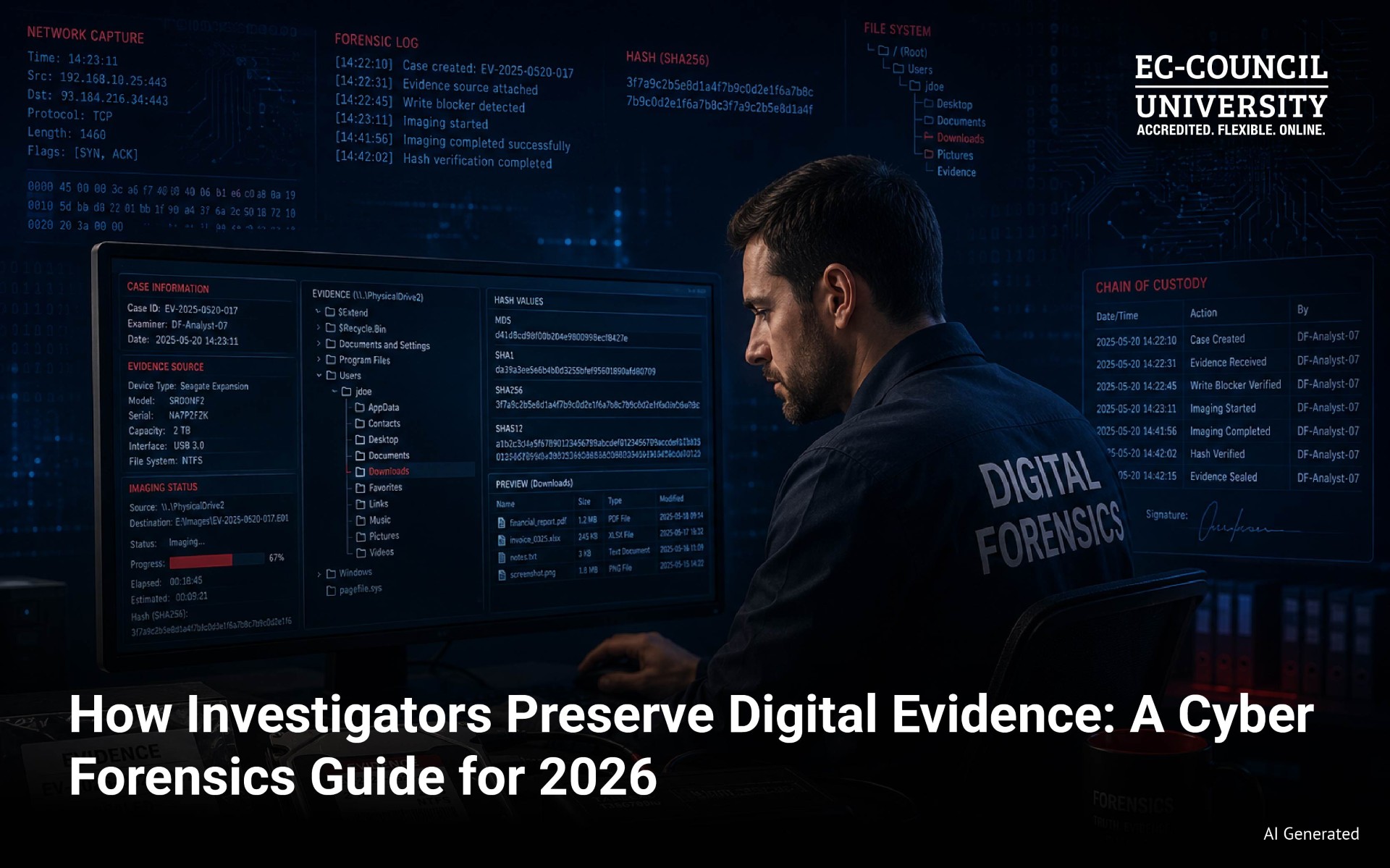
When digital evidence enters an investigation, the clock starts immediately. Every action taken on a device, every file opened, every second of delay changes what

Cybersecurity is no longer a field where broad knowledge carries you to the top. The roles commanding serious compensation in 2026 belong to specialists. Security

Digital forensics has moved well beyond the crime lab. Today it serves incident response teams, litigation support, and corporate intelligence. Organizations in finance, healthcare, and

What Is Disaster Recovery in Cybersecurity? Disaster recovery (DR) in cybersecurity refers to the processes, policies, and technologies used to restore IT systems, data, and

Thinking of a Career Path After Military Service? If you’re a U.S. Military veteran, odds are that you’ve considered online education to help you pursue
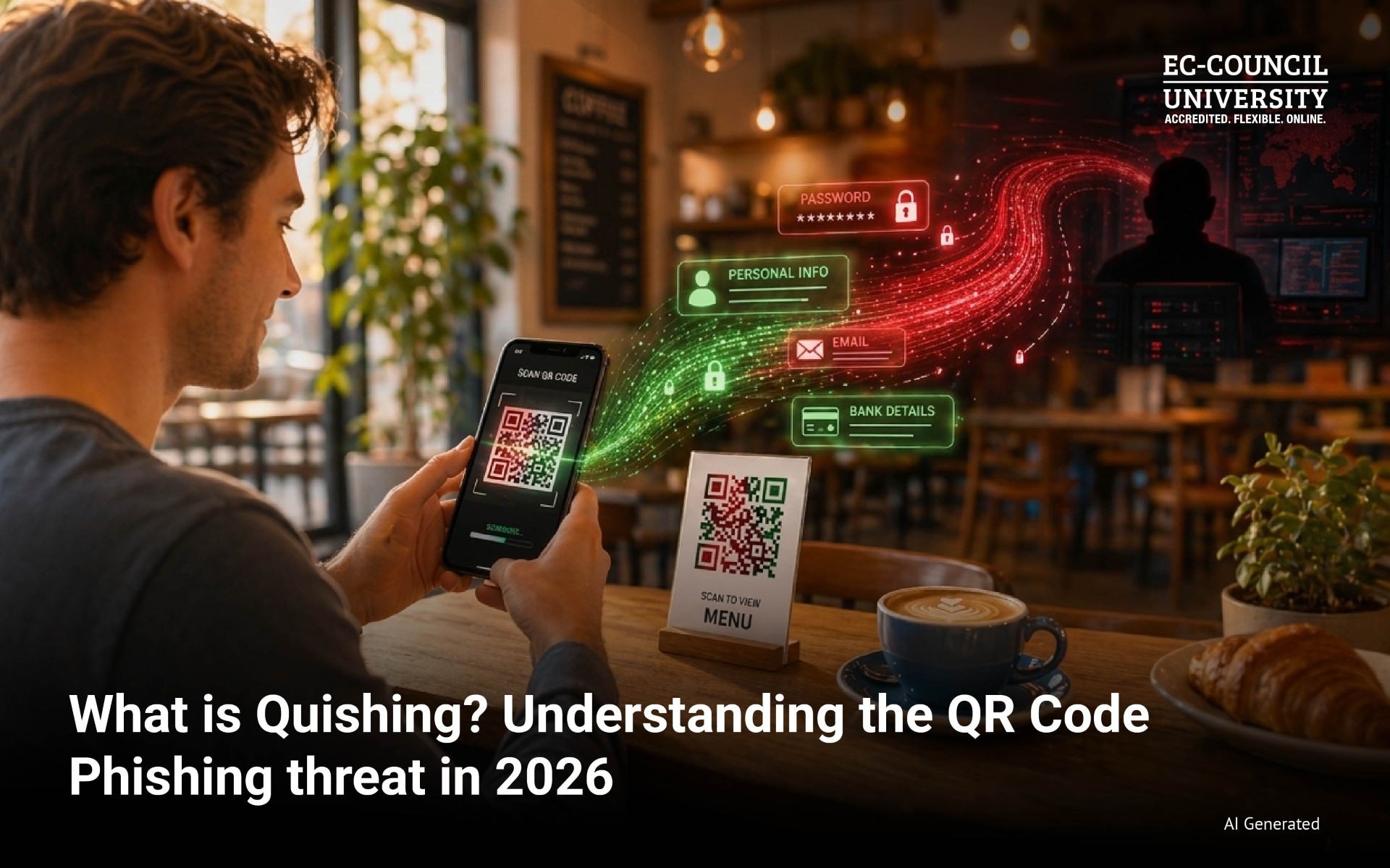
Quishing is not an emerging threat anymore. It is here, and it is scaling fast. What started as a fringe attack technique has quietly grown
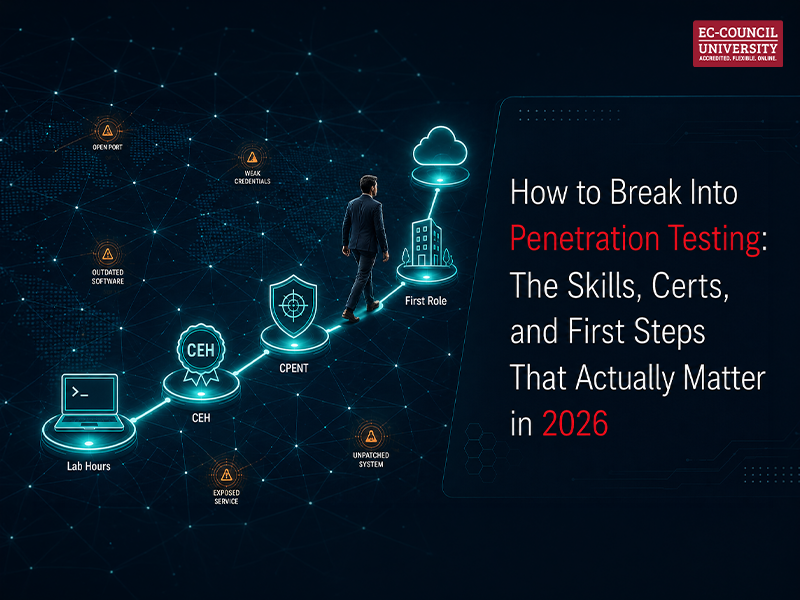
Penetration testing is one of those careers that sounds clear from the outside. You simulate attacks. You find vulnerabilities. You get paid well to think

The Rise of Prompt Injection as a Cybersecurity Threat As organizations race to embed large language models (LLMs) into customer service platforms, enterprise tech stacks,

Cybersecurity is not a static field. It never was. But the pace at which AI is reshaping it has forced a specific question for anyone
Introduction (ICYMI): Escalation, Perception, and the Limits of Control Part 2 examined how cyber conflict extends beyond the digital domain into real-world consequences. We learned that cyber operations are not confined to networks. They can affect critical infrastructure, financial systems, and even physical assets. The Stuxnet example demonstrated that cyber....
Introduction (ICYMI): From Deterrence Breakdown to Continuous Cyber Competition Before examining how cyber conflict escalates, it’s important to revisit the foundation established in Part 1. Traditional deterrence theory assumes a world of clarity, where actors can be identified, intentions are visible, and consequences are predictable. In cyberspace, those assumptions begin....
Cyber Conflict Beyond the Technical Lens Cyber conflict is often framed as a technical issue, centered on vulnerabilities, exploits, and defensive tools. But this perspective misses the bigger picture. Cyber operations are strategic instruments of statecraft, embedded in: Political competition Military planning Global security dynamics To understand their true impact,....
There are 1,757 data breaches each minute. By the time you finish reading this article, thousands of data breaches will have occurred. A person, organization, or government directs most. Local governments struggle to keep up with new technologies for better service in exchange for the risk of a cyber attack....
Responding to cyber threats has become a high priority for organizations of all sizes, especially those in financial services. Cybersecurity is a vital element in preventing cyberattacks, as established in the good practices report published by the Financial Industry Regulatory Authority (FINRA). It is an institution that regulates the activity....
In the rapidly evolving digital landscape, cybersecurity has emerged as a critical concern for organizations across all industries. Understanding and addressing cybersecurity risks is essential for protecting data and ensuring the resilience and continuity of business operations. As a faculty member specializing in human resources, change management, and business continuity....

The demand for cybersecurity professionals has reached unprecedented heights. With the constant proliferation of cyber threats and the crucial need to safeguard sensitive data, there’s a significant shortage of skilled cybersecurity experts. You’re on the right track if you’re considering a career in this dynamic field. This blog is your

1. How does cloud technology help to secure a remote workforce compared to traditional on-premises solutions? Cloud technology has the ability to adapt quicker to changes needed to secure workloads. It can spin up new services/servers to account for increased load during demand. It can also be more highly available

As data becomes more central to businesses, there are more opportunities for compliance violations and a greater risk of breaches. Therefore, data security and privacy have become more critical than ever. Cybersecurity professionals today are effectively entrusted with defending organizations’ data across multiple environments, making the role of a CISO

The dark data industry is rapidly growing, and cyber crimes will only increase in the future. Dark data is generally the data collected as part of compliance but is not effectively used as part of business strategy or marketing. Thus, this type of additional but excessive data that is not












Unlock Your Cyber Security Potential at EC-Council University
"*" indicates required fields
"*" indicates required fields